Crypto security: how to protect your digital assets from hackers

In today’s digital age, crypto security is more crucial than ever. With the rise of cryptocurrencies, the protection of digital assets against hacking and theft has become a top priority for investors. Understanding the fundamentals of crypto security will help you secure your investments effectively.
This article will explore various aspects of crypto security, including best practices, types of scams, and effective strategies to protect your assets.
How Is Crypto Security Defined?
Crypto security refers to the measures taken to protect digital assets, such as cryptocurrencies, from unauthorized access, theft, and cyber threats. This encompasses a variety of strategies, tools, and best practices that individuals and organizations employ to safeguard their investments.
At its core, crypto security involves securing private keys, which are essential for accessing and managing cryptocurrency holdings. Any compromise of these keys can lead to significant financial losses.
Moreover, the security of blockchain technology itself plays a vital role in enhancing the overall safety of digital assets. By ensuring the integrity and transparency of transactions, blockchain technology mitigates risks associated with fraud and hacking.
Why Is Effective Crypto Security Important?
As cryptocurrencies continue to gain popularity, the importance of effective crypto security cannot be overstated. Cybercriminals are constantly devising new ways to exploit vulnerabilities in digital asset management systems.
According to recent statistics, billions of dollars worth of cryptocurrency have been lost due to hacking incidents. Therefore, implementing robust security measures is essential for protecting your investments from potential threats.
In addition to financial loss, a breach in security can damage your reputation and trustworthiness in the crypto community. This makes it imperative for individuals and businesses to prioritize security.
What Are the Types of Cryptocurrency Scams and Risks?
The world of cryptocurrency is rife with scams and risks that can jeopardize your investments. Some common types of scams include:
- Phishing attacks: Cybercriminals impersonate legitimate entities to steal your private keys or login details.
- Investment scams: Promises of guaranteed returns lure investors into schemes that often end in losses.
- Fake exchanges: Fraudulent platforms trick users into depositing funds, which are then stolen.
- Ransomware attacks: Malicious software locks your files until a ransom is paid, often in cryptocurrency.
Understanding these risks is the first step in protecting yourself and your assets. Awareness of common scams can help you make informed decisions and avoid potential pitfalls.
How Can You Protect Your Crypto from Hackers?
To safeguard your digital assets, consider implementing the following best practices for securing your cryptocurrency from theft:
- Use hardware wallets: These devices store your private keys offline, making them less susceptible to hacking.
- Enable two-factor authentication (2FA): Adding an extra layer of security can significantly reduce the risk of unauthorized access.
- Regularly update software: Keeping your wallets and devices updated ensures you have the latest security features and patches.
- Beware of public Wi-Fi: Avoid accessing your wallets or making transactions on unsecured networks.
By following these guidelines, you can enhance your crypto security and minimize the risk of theft or loss.
What Is the Best Way to Secure Your Crypto Wallet?
The best way to secure your crypto wallet involves a combination of techniques that prioritize safety and convenience. Firstly, choose a reputable wallet provider that offers solid security features. Look for wallets that support two-factor authentication, multi-signature functionality, and encryption.
Another crucial aspect is to regularly back up your wallet and store the backup in a secure location. This ensures that you can recover your funds in case of device failure or loss. For added protection, consider using hardware wallets to store large amounts of cryptocurrency.
Lastly, be vigilant about phishing attempts and always verify the authenticity of any software or applications you use to manage your crypto assets.
How to Store Cryptocurrency Offline for Maximum Security?
Storing cryptocurrency offline, also known as cold storage, is one of the most secure methods to protect your digital assets. Hardware wallets are the most popular option for cold storage. These devices keep your private keys offline, reducing exposure to online threats.
Another method involves using paper wallets, where your keys are printed on paper and stored in a safe location. This option, while secure, requires careful handling to prevent loss or damage.
Regardless of the method chosen, the key principle is to ensure that your private keys are not accessible online. This minimizes the risk of hacking and unauthorized access.
What Makes Cryptocurrency Secure Against Cyber Threats?
Several features contribute to the inherent security of cryptocurrencies against cyber threats:
- Decentralization: Most cryptocurrencies operate on decentralized networks, making it difficult for hackers to manipulate the system.
- Blockchain technology: Transactions are recorded on a public ledger, providing transparency and making fraudulent activities easily detectable.
- Cryptographic techniques: These methods ensure the integrity and confidentiality of transactions, protecting against unauthorized access.
While no system is entirely foolproof, these features significantly enhance the security of cryptocurrencies and mitigate risks associated with cyber threats.
Questions related to protecting digital assets from hackers
How to protect your crypto from hackers?
To protect your crypto from hackers, it’s essential to implement comprehensive security measures. Start by using hardware wallets for offline storage, which drastically reduces exposure to online threats. Additionally, always enable two-factor authentication (2FA) on your accounts for an extra layer of security.
Regularly monitor your accounts for any unauthorized activity and stay updated on current phishing scams. Educating yourself on common threats will help you recognize suspicious activities quickly and take appropriate action.
How to lock crypto assets?
Locking crypto assets involves using various security features provided by wallets and exchanges. Most platforms allow you to set withdrawal limits or lock your assets temporarily. Utilizing these features can prevent unauthorized transactions.
Additionally, consider placing your assets in a cold storage solution, such as a hardware wallet. This way, even if your online accounts are compromised, your assets remain secure offline.
What is the golden rule for crypto safety?
The golden rule for crypto safety is to always maintain control of your private keys. Your private keys are the gateway to your assets, and losing control over them can lead to irreversible losses.
Additionally, regularly backup your wallet and use reputable platforms. Ensure you keep your software updated and be cautious about sharing sensitive information.
Which type of crypto wallet is the most vulnerable to hackers?
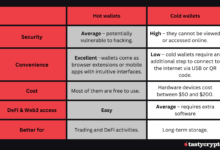
Hot wallets, which are connected to the internet, are the most vulnerable types of wallets. While they offer convenience for transactions, they also expose your assets to hacking risks.
To mitigate these risks, only store small amounts in hot wallets for daily transactions and use hardware wallets for long-term storage. This strategy allows you to enjoy the benefits of quick access while keeping your main holdings secure.